Security Solutions
A Single Source Solution Provider for All Your Security Needs
Security Solutions
Comprehensive security solutions are more than having a firewall in place and a locked front door. The heartbeat of your business is your customer data and financial exposure, and every day we see front page headlines for data breaches, even at Fortune 500 enterprises. Small businesses are attacked daily as well, and often the damages are so devastating that they never recover, both in terms of financial losses and reputation.
We recognize that security is also more than technology… it is about the technical solutions, processes to evaluate and react to potential threats, vulnerabilities, and impacts, plus user training and education.
Key Security Services
- Penetration Testing & Environment Audits
- Full Security Operations Center (SOC) as a Service
- Physical security protection (IP cameras / door entry / video)
- Web and Application Firewall Management
- DDoS Mitigation
- SIEM Platforms & Reporting & Monitoring
- Virus, Malware, Spyware, Email Scanning
- Compliancy Attestations
- IDS/IPS Management
- Endpoint & Device Security Management
- Virtual CISO
- Disaster Recovery and Backups
- Data Loss Prevention (DLP)
- East/West Traffic Monitoring & Breach Protection
- Behavioral Management / Staff Training & Awareness
- Professional Services Security Consulting
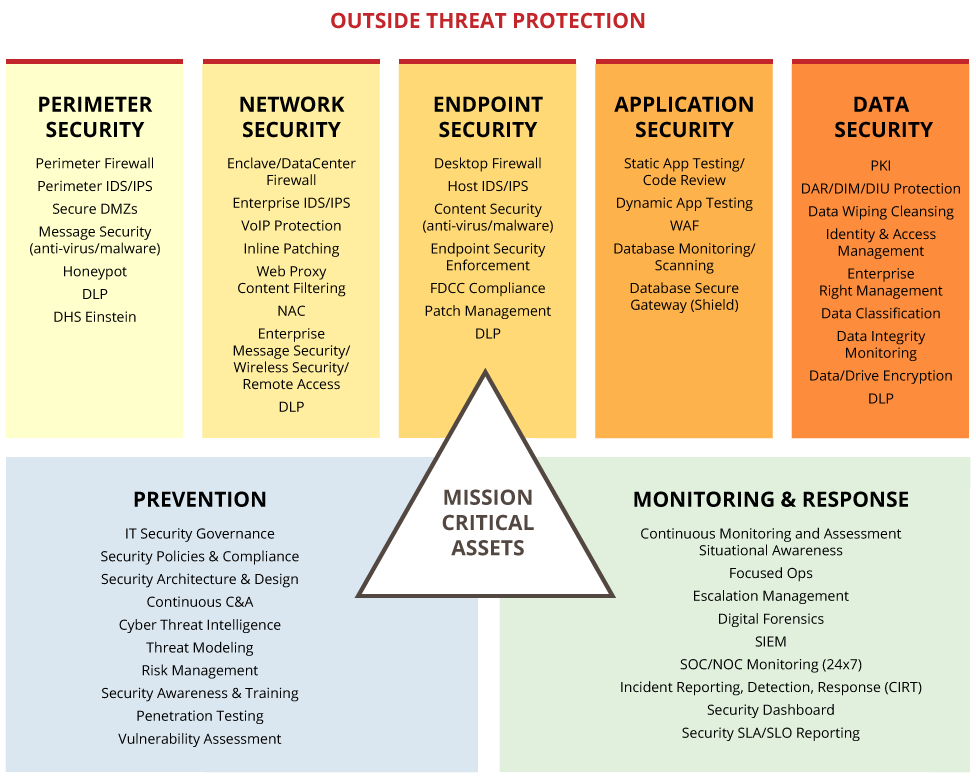
Cyber security and physical security is not just about technology. While technology plays a substantial role, alone it is not enough to protect you from modern vector attacks.
Integritas follows the ISO 27001 standard that recommends every comprehensive security solution address all areas of information security risk including people, process & technology.
By following this standard, we are confident we can help protect your mission critical assets, and bring the solutions required to protect, monitor, and respond to attacks from all vectors – protecting more than just your data and your network, but also your brand
and reputation.
Why work with us?
As Your Solutions Partner, Integritas.
- Objective & vendor agnostic to evaluate multiple security options
- Will learn your business structure and goals
- Will understand your IT infrastructure and vulnerabilities
- Will determine the optimal comprehensive security solution
- Will manage the implementation and support of the selected solution
- After implementation support including customer service and escalations
- Be integrated as part of your organization’s ecosystem
Resources
We share useful industry knowledge.






_Logo_282.png?_cchid=fa39b71e233943de8cc20986401fdb33)




-min.png?_cchid=dfb330c4a8b30ff42ef72c9cfca985e4)





























.jpg?_cchid=0737d43a0c9247da7431da25472e48c8)
